The Benefits of Using a Flow Collection Engine for Network Monitoring As the complexity and scale of network infrastructures continue to grow, so does the […]
How to Use IPFIX for Enhanced Network Visibility
How to Use IPFIX for Enhanced Network Visibility IPFIX (Internet Protocol Flow Information Export) is a protocol that enables network devices and applications to export […]
Implementing a NetFlow-Based Monitoring System
Implementing a NetFlow-Based Monitoring System In today’s networked world, monitoring and analyzing network traffic has become increasingly important for ensuring the security, performance, and reliability […]
Understanding the Importance of Network Traffic Monitoring
Understanding the Importance of Network Traffic Monitoring Network traffic monitoring is a critical aspect of network management that helps administrators understand and manage the flow […]
Using Static Analysis Software to Improve Code Quality and Security
Using Static Analysis Software to Improve Code Quality and Security As software developers, we’re always looking for ways to improve the quality and security of […]
The Benefits of Using a Security Champion Program for Secure Development
The Benefits of Using a Security Champion Program for Secure Development In today’s digital landscape, security is no longer an afterthought in software development. As […]
How to Use Code Review Tools to Identify Security Vulnerabilities
How to Use Code Review Tools to Identify Security Vulnerabilities As developers, we strive to write secure and maintainable code. However, even the most experienced […]
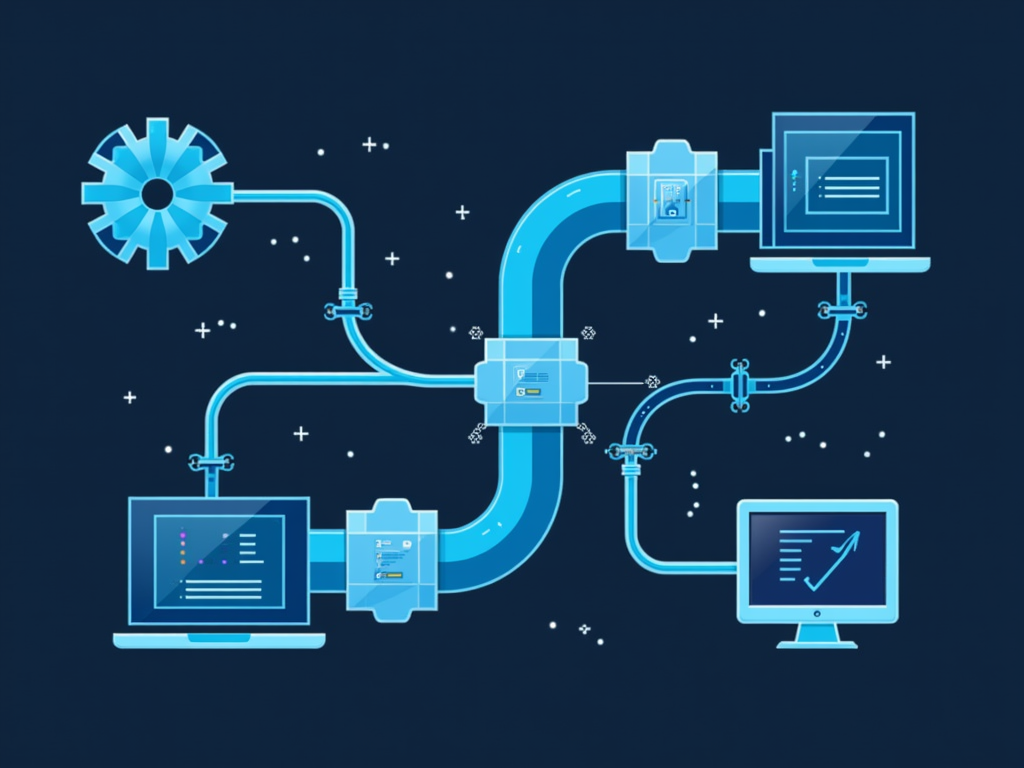
Implementing Secure SDLC Pipelines in DevOps Environments
Implementing Secure SDLC Pipelines in DevOps Environments In today’s fast-paced software development landscape, the importance of implementing secure Software Development Life Cycle (SDLC) pipelines cannot […]
Understanding the Importance of Secure Coding Practices
Understanding the Importance of Secure Coding Practices As developers, we have a crucial role to play in ensuring that our applications are secure and trustworthy […]
Using Artificial Intelligence (AI) to Enhance Incident Response
Using Artificial Intelligence (AI) to Enhance Incident Response Introduction Incident response is a critical aspect of any organization’s emergency preparedness plan. Whether it’s a natural […]