Understanding the Importance of Secure Software Development in Businesses As technology continues to evolve and play an increasingly prominent role in modern businesses, it is […]
How to Use AI-Powered Cybersecurity Solutions for Predictive Analytics
How to Use AI-Powered Cybersecurity Solutions for Predictive Analytics In today’s digital landscape, cybersecurity threats are becoming increasingly sophisticated and rampant. As a result, organizations […]
Implementing an Effective IoT Security Strategy in Smart Cities
Implementing an Effective IoT Security Strategy in Smart Cities Smart cities are transforming the way we live and work, with Internet of Things (IoT) devices […]
Understanding the Rise of Cloud-Based Security Threats in Businesses
Understanding the Rise of Cloud-Based Security Threats in Businesses =========================================================== As businesses increasingly rely on cloud-based services and applications to streamline their operations, they are […]
Using Artificial Intelligence (AI) for Predictive Analytics and Network Security
Using Artificial Intelligence (AI) for Predictive Analytics and Network Security Artificial intelligence (AI) has revolutionized the way we approach data analysis, security, and decision-making. In […]
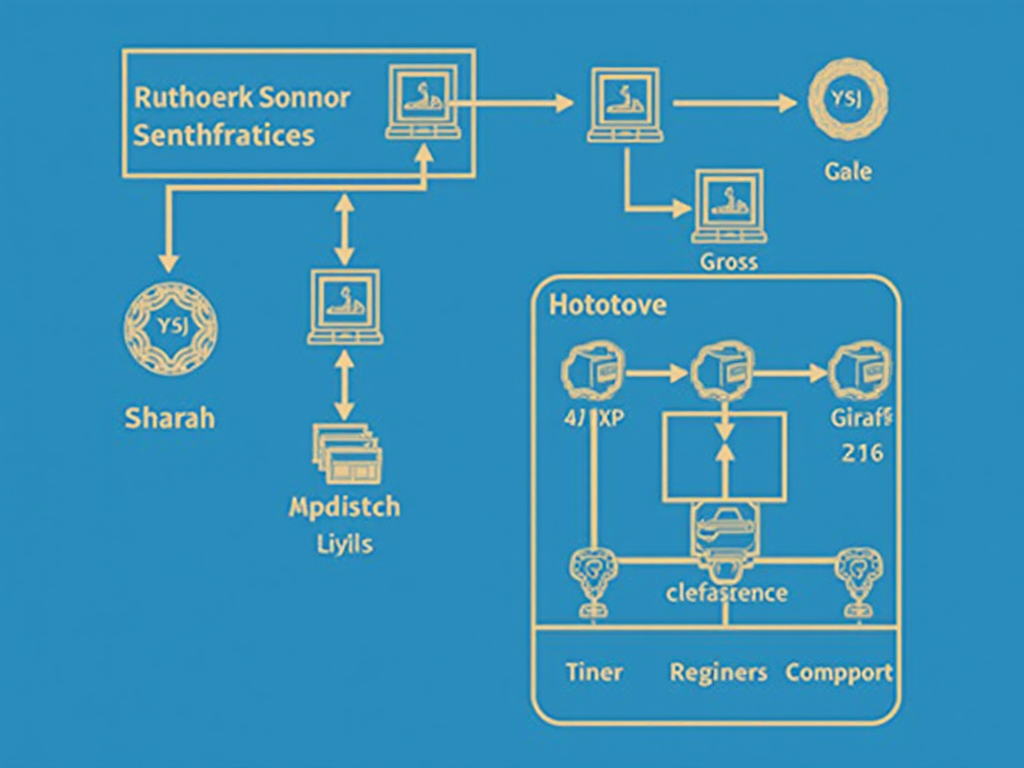
How to Use Network Isolation and Access Control for Security
How to Use Network Isolation and Access Control for Security In today’s digital age, network security is of paramount importance. With the increasing reliance on […]
Implementing an Effective Network Segmentation Policy
Implementing an Effective Network Segmentation Policy Network segmentation is the practice of dividing a network into smaller, isolated segments to control access and improve security. […]
Understanding the Importance of Secure Network Design in Businesses
Understanding the Importance of Secure Network Design in Businesses As businesses continue to rely on digital technologies to drive growth and efficiency, the importance of […]
Using Executive Buy-In for Cybersecurity Initiatives
Using Executive Buy-In for Cybersecurity Initiatives As the importance of cyber security continues to grow, organizations are recognizing the need to prioritize these efforts. One […]
The Benefits of Using a Cybersecurity Steering Committee
The Benefits of Using a Cybersecurity Steering Committee In today’s digital age, cybersecurity is no longer just an afterthought for organizations. With the increasing threat […]