Understanding the Importance of Secure Access in Cybersecurity Introduction In today’s digital age, cybersecurity has become an essential component of any organization’s IT infrastructure. With […]
Using Machine Learning (ML) and AI for Security Automation
Using Machine Learning (ML) and Artificial Intelligence (AI) for Security Automation In today’s digital age, security is a top concern for individuals, organizations, and governments […]
Understanding the Importance of Secure Data Protection in Businesses
Understanding the Importance of Secure Data Protection in Businesses As businesses continue to rely on digital technologies, the importance of securing data protection cannot be […]
The Benefits of Using a Security Orchestration Platform (SOP)
The Benefits of Using a Security Orchestration Platform (SOP) Security orchestration platforms (SOPs) have become an essential tool for organizations to manage their security posture […]
How to Use API-Based Integration for Security Automation
How to Use API-Based Integration for Security Automation As organizations continue to digitize and expand their operations, the need for robust security measures has become […]
Implementing an Effective SOAR System for Incident Response
Implementing an Effective SOAR System for Incident Response As the world becomes increasingly dependent on technology, the importance of effective incident response cannot be overstated. […]
Understanding the Role of Security Automation in Cybersecurity
Understanding the Role of Security Automation in Cybersecurity As cybersecurity threats continue to evolve and become more sophisticated, security teams are under increasing pressure to […]
Using Network Traffic Analysis (NTA) Tools for Security Threat Detection
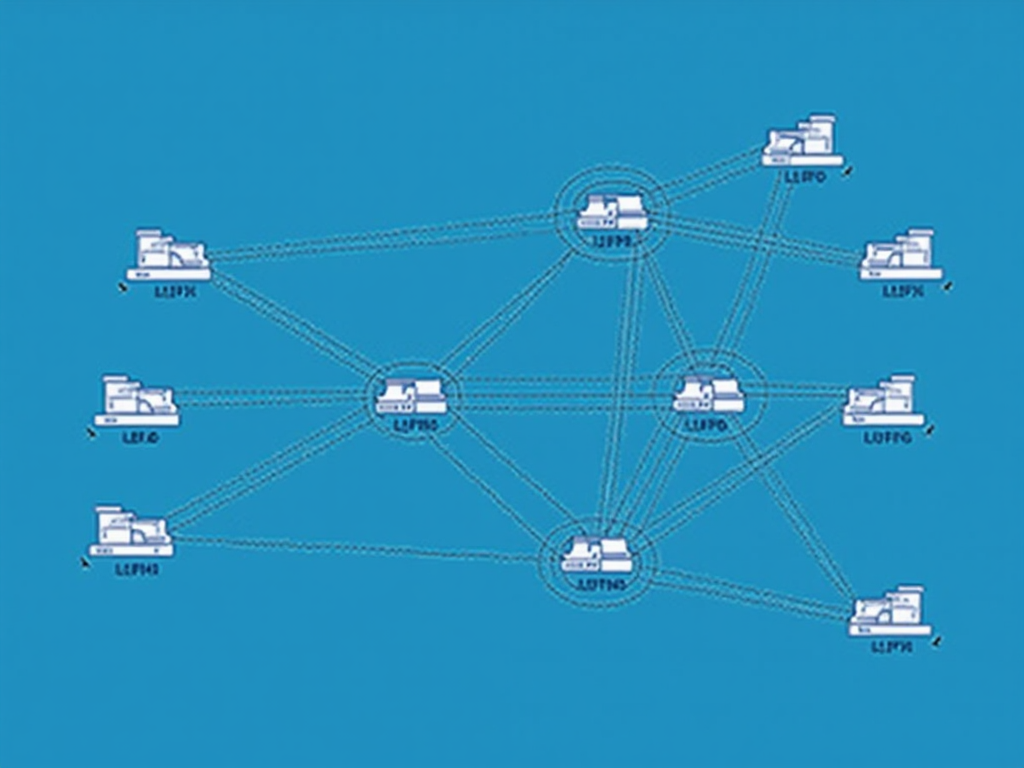
Using Network Traffic Analysis (NTA) Tools for Security Threat Detection Network traffic analysis (NTA) tools are powerful solutions that help organizations detect and respond to […]
The Benefits of Using a Flow Collection Engine for Network Monitoring
The Benefits of Using a Flow Collection Engine for Network Monitoring As the volume and complexity of network traffic continues to grow, network administrators face […]
How to Use IPFIX for Enhanced Network Visibility
How to Use IPFIX for Enhanced Network Visibility As network administrators, we’re constantly striving to gain deeper insights into our network’s behavior and performance. One […]